Data enrichment fraud is a deceptive practice that can have a significant impact on businesses. It involves the manipulation or falsification of data during the data enrichment process, aiming to deceive or defraud organizations. Data enrichment, on the other hand, is a valuable tool used by businesses to enhance their datasets with additional information for improved insights and decision-making. However, when fraudulent data enrichment occurs, it can lead to misleading insights, damaged customer relationships, wasted resources, compliance risks, and reputational damage. Let’s delve into the concept of data enrichment fraud, its impact on businesses, strategies to identify and detect fraud, prevention measures, and what to do if you suspect data enrichment fraud has occurred. Understanding and addressing this issue is crucial for maintaining data integrity, safeguarding business operations, and protecting customer trust.
Data enrichment fraud refers to the act of manipulating or falsifying data during the process of data enrichment in order to deceive or defraud a business or organization. Data enrichment involves enhancing existing datasets with additional information to gain deeper insights, improve decision-making, or enhance marketing efforts. This additional information can include demographic details, behavioral patterns, social media profiles, purchase history, and more.
Data enrichment is a valuable tool for businesses as it helps them better understand their customers, personalize marketing campaigns, and improve overall operational efficiency. However, when fraudulent data enrichment occurs, it can have several negative impacts on a business’s success:

- Misleading insights: Fraudulent data enrichment can introduce inaccurate or false information into a business’s datasets. This can lead to misleading insights and decisions based on unreliable data, affecting the effectiveness of marketing strategies, customer segmentation, and overall business planning.
- Damaged customer relationships: Fraudulent data enrichment can result in incorrect customer profiles or inaccurate customer preferences. This can lead to misguided marketing efforts, irrelevant offers, or intrusive communications, which may frustrate or alienate customers. Consequently, businesses risk damaging their relationships with customers and losing their trust.
- Wasted resources: Investing in data enrichment processes can be costly. If the enriched data is fraudulent, businesses waste valuable resources on acquiring and analyzing misleading information. This can lead to ineffective marketing campaigns, poor customer targeting, and inefficient resource allocation, negatively impacting a company’s bottom line.
- Compliance and legal risks: Fraudulent data enrichment may involve obtaining and using data through illegal or unethical means, such as purchasing data from unauthorized sources, engaging in identity theft, or violating privacy regulations. Businesses that engage in or unknowingly use fraudulently enriched data can face severe legal consequences, including fines, legal disputes, damage to reputation, and loss of customer trust.
- Reputation damage: If a business is found to be using fraudulent data or engaging in data enrichment fraud, its reputation can suffer significantly. Customers, partners, and stakeholders may view the business as untrustworthy, leading to a loss of credibility and potential loss of business opportunities.
To mitigate the impact of data enrichment fraud, businesses should prioritize data quality assurance measures, including robust data validation processes, source verification, and regular audits. It is essential to establish strict data acquisition policies, ensuring compliance with relevant regulations and ethical standards. Additionally, maintaining transparency with customers and informing them about data usage and protection practices can help build trust and minimize reputation damage.
There are many strategies a company can use to effectively identify and detect fraud in their data enrichment practices. One key approach is to look for inconsistencies within the enriched data. By comparing the new data with existing records, businesses can identify any discrepancies or contradictions that may indicate fraudulent data enrichment. For example, if a customer’s purchase history shows a sudden increase in transactions without corresponding indicators of increased engagement, it could be a red flag.
Another important strategy is to check the sources of the enriched data. It is crucial to scrutinize the credibility and reputation of the data providers or vendors. Businesses should ensure that these providers adhere to ethical practices and comply with relevant data protection regulations. By conducting due diligence, businesses can confirm the legitimacy and reliability of the data sources.
Additionally, it is essential to independently verify the accuracy and authenticity of the enriched data. This can be done by cross-referencing the data with multiple reliable sources or conducting independent data collection. For example, if your data provides demographic details, verifying them through other trustworthy data enrichment sources like official government records or DaaS companies, like Endato, can help validate the information.
Employing data analysis techniques is another effective approach. By analyzing patterns within the enriched data, businesses can identify suspicious anomalies or patterns that do not align with expected behaviors. Statistical analysis, data visualization, and machine learning algorithms can be utilized to detect outliers, unusual behaviors, or data clusters that may indicate fraudulent data enrichment. Regularly conducting internal and external audits of data enrichment processes is crucial. These audits should thoroughly examine the data sources, data collection methods, and data enrichment techniques. By evaluating the controls in place, businesses can ensure data integrity and assess the accuracy and reliability of the enriched data. Independent auditors or data analytics specialists can provide an objective assessment of the data enrichment practices.
Implementing fraud detection tools and technologies designed specifically for identifying fraudulent activities in data can significantly enhance fraud detection efforts. These tools utilize algorithms and machine learning models to identify suspicious patterns, anomalies, or data manipulation techniques. They can automate the detection process and provide real-time alerts when fraudulent data enrichment is detected. When continuously monitoring the quality of enriched data, it’s important for businesses to establish robust data quality assurance processes. This includes implementing data validation techniques such as data cleansing and data profiling to ensure data accuracy, completeness, and consistency. Regular monitoring and measurement of data quality metrics help identify any deviations or inconsistencies that may indicate fraudulent data enrichment.
By employing these strategies, businesses can enhance their ability to detect and prevent fraud in data enrichment. Timely identification of fraudulent activities allows businesses to take corrective measures, safeguard their operations, and maintain the integrity of their data-driven decision-making processes.
Endato offers a variety of tools to help with data enrichment, such as contact enrichment, callerID, AddressID, EmailID. These tools can help with data enrichment by adding more information to existing data.
Contact Enrichment API can be used to add additional information to contact records, such as social media profiles, employment information, and more. This can help businesses better understand their customers and target their marketing and communication efforts more effectively. By integrating with the Contact Enrichment API, businesses can ensure that their contact data is always up-to-date and accurate.
CallerID can be used to identify the owner of a phone number and provide additional information about them, such as their name, address, and social media profiles. This can be useful for businesses that rely on phone communication to reach their customers, as it can help them better understand who they are talking to and tailor their communication accordingly.
AddressID can be used to verify and enrich address data by adding missing information, such as geolocation data or building information. This can help ensure that address data is accurate and up-to-date, which is important for businesses that rely on accurate address data for shipping, logistics, and customer communication.
EmailID can be used to identify the owner of an email address and provide additional information about them, such as their social media profiles and job title. This can be useful for businesses that use email communication to reach their customers, as it can help them tailor their communication to the recipient’s interests and needs.
Depending on your companies needs, you can find the right tools for your data enrichment solutions on our Developer API page, where you can browse a full list of Endato API products.
If you suspect data enrichment fraud has occurred with your business’s data, it is important to take immediate action to address the issue. The most important steps to take are to investigate the issue, and take corrective action for the problems that are found, here’s some step-by-step tips on how to put that plan into action:
Investigate the issue:
- Thoroughly analyze the data: Examine the enriched data sets and look for any inconsistencies, anomalies, or suspicious patterns. Identify specific records or data points that may be affected by fraudulent activities.
- Interview relevant individuals: Speak with employees, contractors, or individuals involved in the data enrichment process to gather information and understand their roles and responsibilities. Ask specific questions about the enrichment process, data sources, and any potential irregularities they may have noticed.
- Review policies and procedures: Assess your existing policies and procedures related to data enrichment. Identify any potential vulnerabilities or gaps that may have allowed fraudulent activities to occur. Determine if there were any deviations from established protocols or if any individuals bypassed security measures.
- Preserve evidence: As part of the investigation, ensure that you preserve all relevant evidence related to the suspected fraud. This includes data records, communication logs, and any other documentation that may help in the investigation.
Take corrective action:
- Report to authorities: If the fraudulent activity involves illegal actions or violates privacy regulations, report the incident to the appropriate authorities, such as law enforcement agencies or data protection authorities. Provide them with all relevant information and evidence you have gathered during the investigation.
- Update policies and procedures: Revise your data enrichment policies and procedures to address any identified vulnerabilities or gaps. Implement additional security measures and controls to prevent future fraud. Ensure that all employees are aware of the updated policies and provide necessary training to mitigate the risk of similar incidents.
- Terminate contracts or employment: If individuals or third-party vendors are found to be involved in the fraudulent activity, terminate their contracts or employment, as applicable. Take appropriate legal steps to recover any losses incurred due to the fraud.
- Revise enriched data sets: Remove any fraudulent data from your enriched data sets to ensure data integrity. Take steps to validate and cleanse the data to restore accuracy and reliability. Consider conducting a re-enrichment process using legitimate data sources to replace any fraudulent or unreliable information.
Remember to consult with legal professionals and follow your organization’s internal protocols when handling suspected data enrichment fraud. Prompt action and thorough investigation will help mitigate the impact of fraudulent activities, protect your business’s reputation, and reinforce the integrity of your data-driven decision-making processes.
Data enrichment fraud is a serious threat that can have significant consequences for businesses. The manipulation or falsification of data during the data enrichment process can lead to misleading insights, damaged customer relationships, wasted resources, compliance risks, and reputational damage. Preventing and addressing data enrichment fraud requires a proactive approach and the implementation of various strategies.
By taking the correct steps, businesses can mitigate the impact of data enrichment fraud, safeguard their operations, and protect the trust of their customers and stakeholders. Prioritizing data integrity and implementing robust fraud prevention measures are essential for maintaining the reliability of data-driven decision-making processes and preserving the reputation of the business.

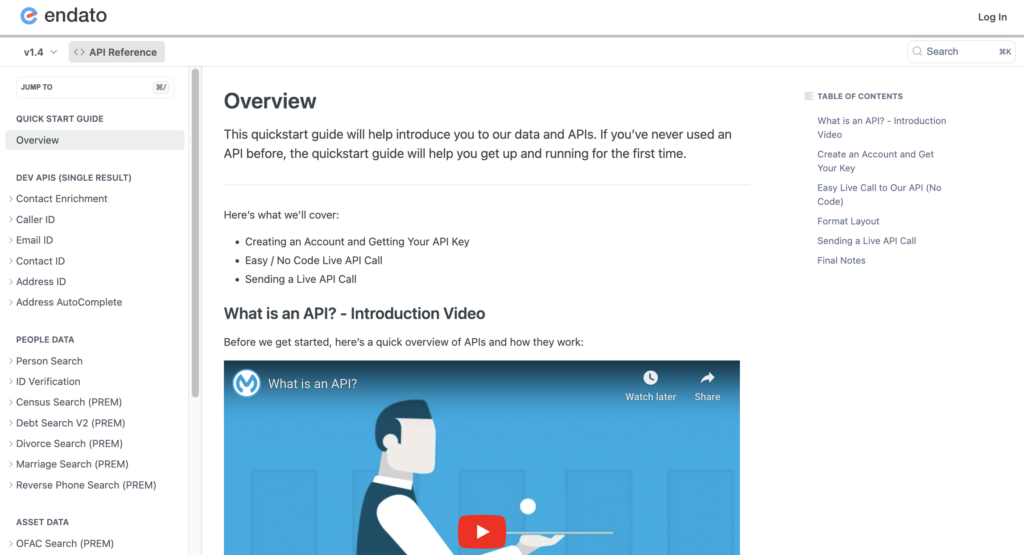
Getting familiar with how to use Endato’s search and API products is very helpful in deciding what products you’ll want to use. We’ve created this quick start guide to walk new users through how to use Endato. Happy searching!